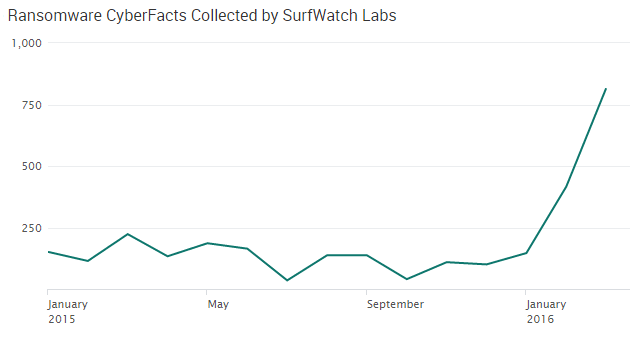
In early 2015, the FBI issued a warning about the rise of ransomware attacks, noting that “there’s been a definite uptick lately in its use by cybercriminals.” A year after that warning we’re seeing a new surge in attacks, and concern over ransomware has risen sharply in the first quarter of 2016.
Last year, the FBI explained that ransomware was continuing to evolve, writing that in the past “computers predominately became infected with [ransomware] when users opened e-mail attachments that contained malware.” That tactic had shifted and computers were now being easily infected using a “drive-by” method “where users can infect their computers simply by clicking on a compromised website, often lured there by a deceptive e-mail or pop-up window.”
The way cybercriminals demand ransom payments has also evolved. Initially, cybercriminals asked for ransom payments on pre-paid cards. Now Bitcoin has been implemented, a better option for criminals “because of the anonymity the system offers.”
SurfWatch Labs’ data identified 49 companies associated with ransomware attacks so far in 2016, although the total number of companies affected by this threat is likely much higher as many companies do not disclose these attacks — particularly if they choose to pay the ransom.
The healthcare sector in particular has been a focus of ransomware discussion this year.
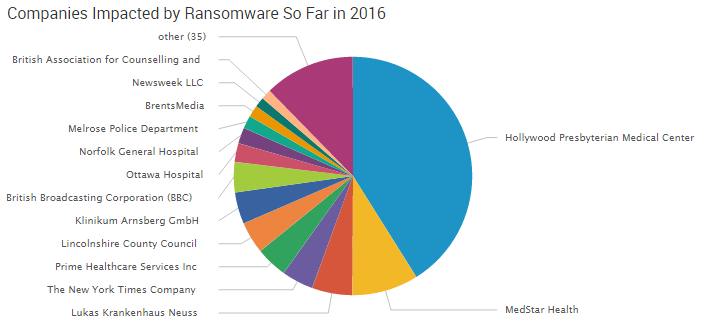
The reason ransomware has continued to gain popularity is simple — it is a cheap tool that has a high profit margin. Not long ago, malware developers were selling Cryptolocker ransomware kits with source code included for just $3,000. It wouldn’t take long for a criminal to recoup that initial investment as the average ransom demand is anywhere from $300 to $500. Recently, Hollywood Presbyterian Hospital reportedly paid $17,000 after suffering a ransomware attack.
Trending Ransomwares in 2016
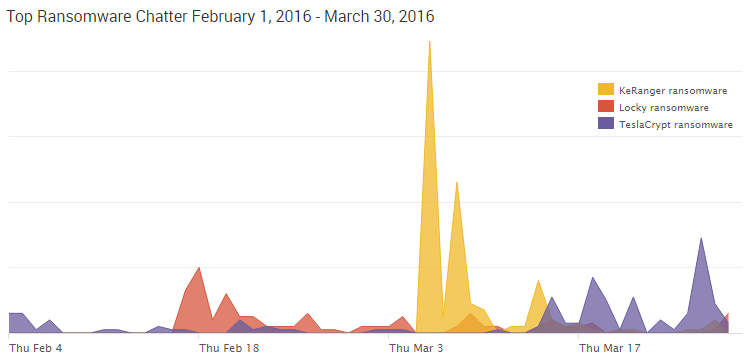
There are three variants of ransomware that have stood out in the beginning of 2016: KeRanger, TeslaCrypt and Locky.
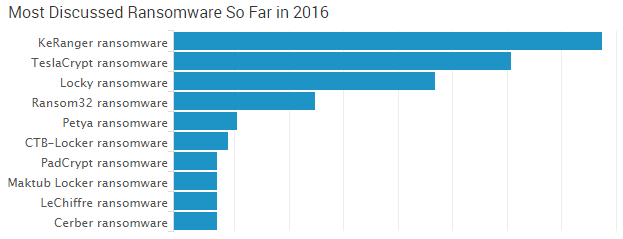
KeRanger malware has received a lot of discussion due to its connection with Apple. Locky ransomware has been observed in several attacks in 2016, and TeslaCrypt, which has been around for more than a year, continues to evolve.
KeRanger Ransomware
The newest addition on the list, KeRanger Ransomware, first made headlines in the beginning of March due to its accomplishments. It is the first ever fully functional Mac OS X ransomware in existence.
KeRanger was able to successfully infect a BitTorrent client used on OS X known as Transmission. More specifically, it infected Transmission version 2.90. Transmission has since warned users that version 2.90 was malicious and prompted users to download version 2.91.
TeslaCrypt Ransomware
TeslaCrypt Ransomware initially made headlines back in early 2015 for infecting computer gamers. Over the last year, TeslaCrypt has continued to evolve, with the latest version TeslaCrypt 4.0 released earlier this month. The ransomware is now capable of attacking organizations and home users.
The latest edition of TeslaCrypt features RSA 4096 for encrypting data. This feature makes decrypting data impossible. Tools developed to combat previous TeslaCrypt versions, such as “TelsaDecoder,” will not work with TeslaCrypt 4.0.
TeslaCrypt ransomware has evolved quickly. In just over a year, malware creators have been able to release four versions of the ransomware, each more sophisticated than the last version. If any weaknesses are found in TeslaCrypt 4.0, look for malware creators to move quickly in creating a new version addressing those weaknesses.
Locky Ransomware
Locky ransomware was discovered in February 2016. The ransomware works like most strains: it infects a user’s computer, encrypts the content on the computer, and then a ransom is extracted in order to decrypt the information. It is in the encryption step that the ransomware gets its name, as it renames all the user’s files with the extension .locky.
This ransomware is being distributed through malicious macros in Microsoft Word attachments. In typical cases, victims receive a spoofed email with a Microsoft Word attachment seeking some sort of payment for a service or product. When the attachment is clicked, a document appears with scrambled text. The user is then instructed to click an Office macro to unscramble the text, which leads to infection.
This ransomware variant made huge headlines for causing Methodist Hospital of Henderson, Kentucky, to declare an “internal state of emergency.” Fortunately, Methodist Hospital was able to regain their data without paying the cybercriminal’s ransom demand of four bitcoins ($1,600).
Being Prepared is Key
Although ransomware has been making headlines for the last few years, data from 2016 suggests more criminals are going to focus on this tactic and more organizations are going to be victimized. Businesses need to be aware of this threat and take action now to mitigate the effects of a potential attack.
As recent attacks have shown, the overall cost of a ransomware attack can be much greater than just the ransom demand.


3 thoughts on “Ransomware Making Headlines In Early 2016”