The massive distributed denial-of-service (DDoS) attack that disrupted websites and services on October 21 was the focal point of a large portion of cybercrime discussion last week. As we noted in a previous post, the attack against DNS provider Dyn has led to widespread concern about insecure Internet-connected devices and calls for government agencies to get involved in order to ensure those devices are secured against future attacks.
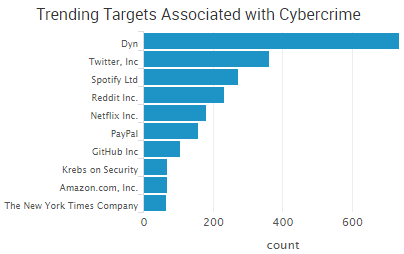 According to some reports, the DDoS attack may have surpassed one terabyte per second of traffic; however, the latest analysis from Dyn indicates that the botnet behind the attack may have been much smaller than the initial reports of “millions.”
According to some reports, the DDoS attack may have surpassed one terabyte per second of traffic; however, the latest analysis from Dyn indicates that the botnet behind the attack may have been much smaller than the initial reports of “millions.”
“It appears the malicious attacks were sourced from at least one botnet, with the retry storm providing a false indicator of a significantly larger set of endpoints than we now know it to be,” wrote Scott Hilton, EVP of products at Dyn. “We are still working on analyzing the data but the estimate at the time of this report is up to 100,000 malicious endpoints. We are able to confirm that a significant volume of attack traffic originated from Mirai-based botnets.”
Other trending DDoS news includes the Syrian Cyber Army claiming responsibility for attacks against Belgian news organizations. The DDoS attacks made several news websites inaccessible or extremely slow, including De Standaard, Het Nieuwsblad, Gazet van Antwerpen, Het Belang van Limburg and RTFB. In another case of ideological hacktivism, Martin Gottesfeld, 32, was indicted for his role in DDoS attacks against Boston Children’s Hospital (BCH) and the Wayside Youth and Family Support Network. Gottesfeld admitted to his involvement in #OpJustina in a written editorial, saying that the attack against BCH was designed to interfere with a fundraiser in order to cause maximum financial damage. Finally, The Guardian is reporting that financial institutions in London are stockpiling bitcoins in the event extortionists target them with powerful DDoS attacks.
Other trending cybercrime events from the week include:
- Payment card breaches announced: Danish payment processor Nets is warning of a payment card breach that appears to be tied to a foreign-based Internet retailer and is advising banks to block up to 100,000 cards in order to prevent fraudulent transactions. A data breach at Hitachi Payment Services, which manages ATM network processing for Yes Bank, is suspected to be the cause of recent fraud that has led to banks in India either replacing or asking customers to change security codes on 3.25 million debit cards. A pro-Donald Trump super PAC known as Great America PAC has mistakenly published the credit card numbers and expiration dates of 49 donors. Last month the same super PAC exposed 336 donors’ email addresses and phone numbers.
- Data breaches continue, both large and small: A Red Cross Blood Service database of 1.28 million donor records going back to 2010 was accidentally published to a webserver by a third-party contractor. A hacker known as Peace told Motherboard he hacked Adult FriendFinder and obtained a database of 73 million users, and another hacker known as Revolver or 1×0123 posted screenshots appearing to show he had access to the website’s infrastructure. A Ukrainian hacker group known as CyberJunta has released more than a gigabyte of emails stolen from the office of Russian politician Vladislav Surkov. Baystate Health is notifying about 13,000 patients that their personal information may have been compromised due to a phishing attack that was designed to look like an internal memo. Virgin Media potentially exposed the personal information of up to 50,000 people applying for jobs. Rocky Mountain Credit Union in Montana notified 135 of its members that their personal information may have been accidentally exposed due to an undisclosed security issue discovered on the website customers use to upload documents related to mortgage applications. The University of Santa Clara’s Office of Marketing and Communications had internal documents stolen and leaked to the student newspaper due to an employee leaving his or her username and password in plain site at a workstation.
- Update on cybercrime charges and arrests: The Booz Allen Hamilton contractor who was arrested for the possession of classified NSA materials allegedly had documents dating back to 1996 that were marked either “secret” or “top secret,” according to recent court filings. In total, investigators have seized more than 50 terabytes of information and thousands of pages of documents. Celebgate hacker Ryan Collins, 36, of Lancaster, Pennsylvania, was sentenced to 18 months in prison for using phishing emails designed to steal Apple and Google credentials and then using those stolen credentials to hack into more than 100 accounts. Authorities said there is no evidence that Collins was responsible for the leak of nude celebrity photographs tied to the hack. Yevgeniy Nikulin, the Russian man who was arrested in connection with the 2012 LinkedIn breach, has also been indicted for his alleged role in the breaches at Dropbox and Formspring, according to documents unsealed on Friday.
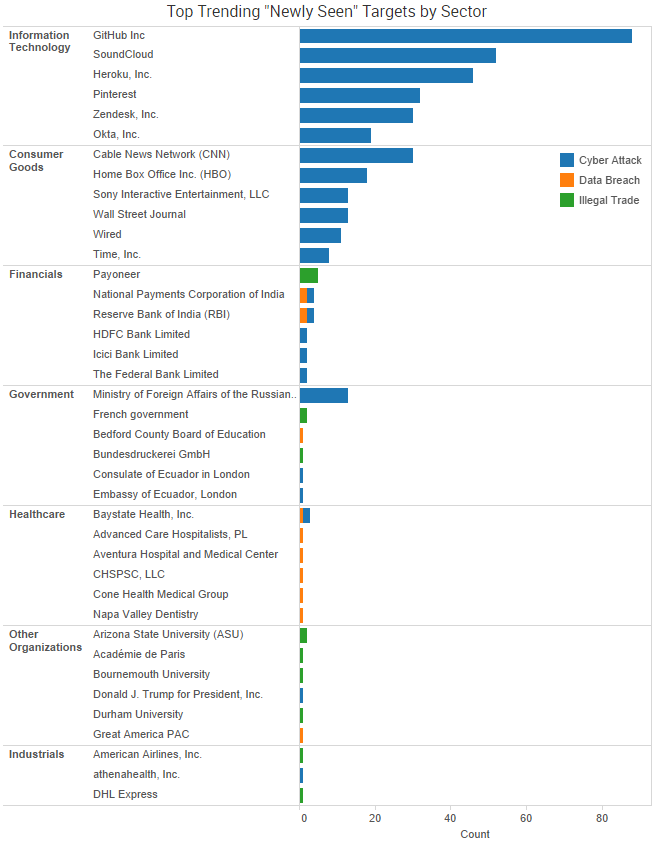
SurfWatch Labs collected data on many different companies tied to cybercrime over the past week. Some of those “newly seen” targets, meaning they either appeared in SurfWatch Labs’ data for the first time or else reappeared after being absent for several weeks, are shown in the chart below.
Note: Dyn, by far the top trending new target, is not shown in the chart below in order to make the other targets more readable.
Cyber Risk Trends From the Past Week
The Financials sector’s cyber risk score peaked in early October, reaching its highest level since February 2016. Since then, it has steadily declined for most of the month — until the past week. This week’s rise in cyber risk score (+2.2%) was the biggest increase of any sector over the period.
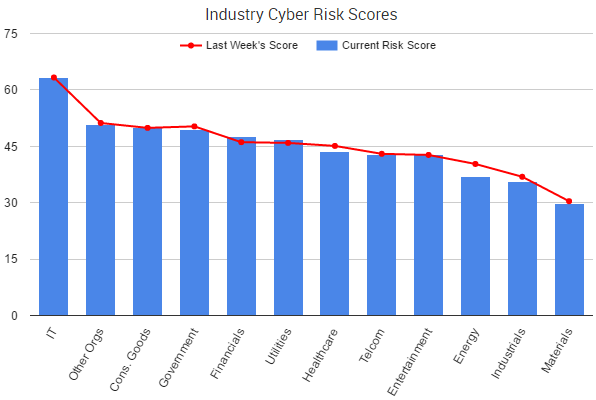
Part of that may be tied to the recent payment card breaches highlighted above, which began at online retailers and other providers before moving to directly impact banks. For example, the chief executive of National Payments Corp of India said that the spike in reported fraud that led to advising banks to replace cards was tied to a possible compromise of one of the payment switch provider’s systems. Sources told Reuters that the issue stemmed from a breach in systems of Hitachi Payment Services, which is currently investigating the matter.
That interconnectivity of the Financials sector has led to concerns from government agencies, and the the Board of Governors of the Federal Reserve System, the Office of the Comptroller of the Currency and the Federal Deposit Insurance Corporation recently issued a joint proposal on enhanced cyber risk management standards to address those concerns.
“Due to the interconnectedness of the U.S. financial system, a cyber incident or failure at one interconnected entity may not only impact the safety and soundness of the entity, but also other financial entities with potentially systemic consequences,” the proposal stated. “The enhanced standards would be designed to increase covered entities’ operational resilience and reduce the potential impact on the financial system in the event of a failure, cyber-attack, or the failure to implement appropriate cyber risk management.”
The proposal addresses five categories of cyber standards: cyber risk governance; cyber risk management; internal dependency management; external dependency management; and incident response, cyber resilience, and situational awareness.
According to the proposal, “The agencies are considering establishing a two-tiered approach, with the proposed enhanced standards applying to all systems of covered entities and an additional, higher set of expectations, or ‘sector-critical standards,’ applying to those systems of covered entities that are critical to the financial sector.”
The enhanced standards would apply to certain entities with total consolidated assets of $50 billion or more on an enterprise-wide basis, they added. Comments on the proposal are open until January 17, 2017.


One thought on “Weekly Cyber Risk Roundup: Latest Breaches and Enhanced Security Standards”