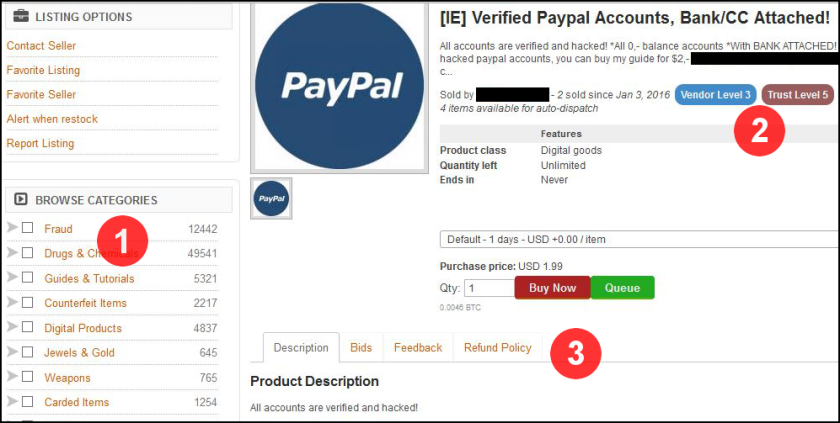
As cyber incidents proliferate, security experts continue to stress the importance of cyber risk strategy starting at the top of organizations. However, a recent report surveying more than 1,500 non-executive directors, C-level executives, Chief Information Officers, and Chief Information Security Officers found that some organizations still have a big knowledge gap when it comes to cyber threats.
According to The Accountability Gap: Cybersecurity & Building a Culture of Responsibility:
-
Only 10% of high vulnerable respondents agree that they are regularly updated about pertinent cybersecurity threats
- More than 90% of high vulnerable board members say they can’t interpret a cybersecurity report
-
Only 9% of high vulnerable board members said their systems were regularly updated in response to new cyberthreats
Many of these organizations are concerned about potential cybercrime. All of them are likely doing something to combat cyber risks. But they’re not getting updated on important threats, they cannot understand the updates that do come through, and as a result they do nothing.
That led me to wonder if we’ve all gotten stuck in the same methods of looking at the same things in the same way day after day without ever taking a breath and a step back and asking, “Wait, why am I doing this?”
The Penny Test
There was a fascinating story on the news awhile back about people getting wrongfully convicted based on faulty eyewitness testimony.
In fact, according to the Innocence Project, “Eyewitness misidentification is the single greatest cause of wrongful convictions nationwide, playing a role in 72% of convictions overturned through DNA testing.”
However, the point wasn’t that eyewitnesses are being careless or that they are just plain ignorant, it’s that without having the whole picture — the complete context of the situation — it’s natural to make a simple mistake that can cost a person decades of his or her life.
To illustrate, let’s do a variation of the Penny Test using a six person “lineup” to see if you can identify the “real” penny.

If you’re like most people, you’ll eliminate a few possibilities, narrowing it down to a couple of choices. Then, over time — and along with other factors that may reinforce your decision — you grow more certain that, yes, that penny you’ve chosen is definitely the right one.
But here’s the problem with the story I’ve given you: it’s incomplete. I failed to mention the possibility that the correct version of the penny might not be there at all.
That’s one of the problems with the human mind, it wants to pick something, and it’s one of the many problems that can arise from eyewitness identification.
All of the pennies were wrong.
Cybersecurity Blind Spots
That lack of context can also be a real problem when it comes to managing cyber risk. Without having the whole picture, it’s natural to invest in the wrong areas or to make a mistake that leaves an organization vulnerable to cyber-attack.
This is what many of the recent studies and surveys have been reinforcing. The IT team is wasting their time elbows deep in low-level data and investigating red flags, never having a chance to think about or act on a high-level strategy. Executives don’t even know what aspects of their company are at risk, so they’re fumbling around in the dark and relying on vendors for the answers.
The problem with that? They’re biased.
Just as the cops in the world of traditional crime may lead a subject towards a certain perpetrator (“We thought it may have been number three too.”), a vendor may lead you towards their biases — regardless of the true risk profile and needs of your business.
When you’re assessing cyber risk, remember that one option is always “none of the above.” The answer might be something else entirely.
Understanding Complete Context
Many organizations have these cyber blind spots. For example, most organizations don’t assess the security of third-party partners or their supply chain, yet we’ve seen dozens of data breaches that begin from these very avenues.
If relevant cyber threat information is available, it often doesn’t make its way to those with the ability to actually make changes. And if it does get passed along, those executives may be unable to interpret the technical language of the threats. And if they do know and understand the threats, it may end up that those threats are no longer as relevant; there may be newer, more pressing cyber risks.
That’s why nearly every cybersecurity best practice guide or cyber risk management program beings with the same thing: context. Clear away as many of those blinds spots as possible.
Remember the Penny Test. Just because you are doing something doesn’t mean it’s the best use of resources. The real threat might still be out there, and without having complete context around your cyber risks, you may miss it.