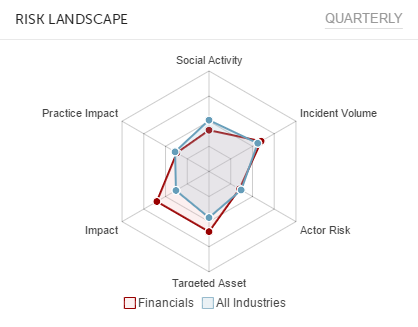
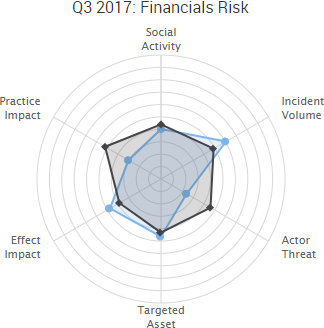
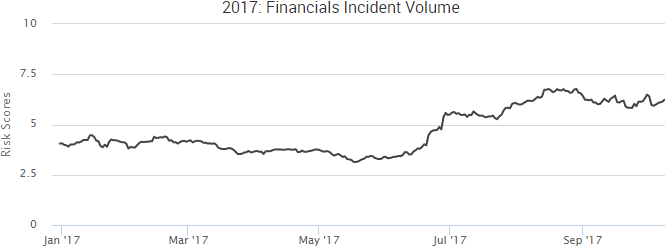
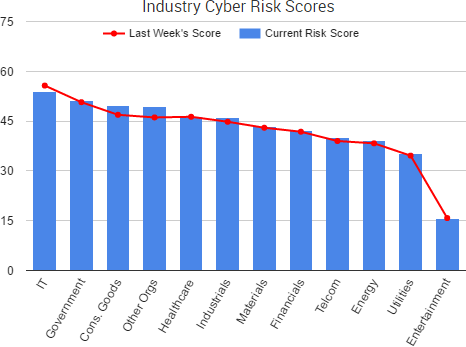
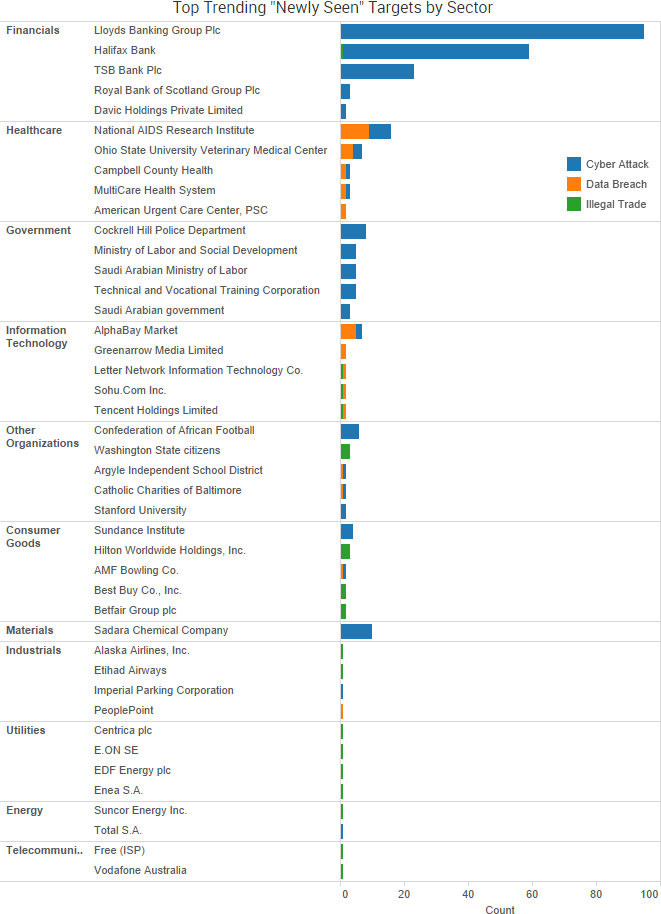
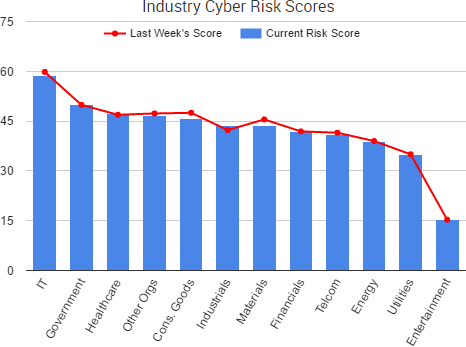
The financials sector saw an increase in incident volume in the third quarter of 2017, and much of that increase revolved around cyber-attacks targeting various cryptocurrency platforms, as well as payment card breaches in the consumer goods sector that led to increased fraud activity on cybercriminal markets.
Key takeaways from SurfWatch Labs’ threat intelligence findings for the period include:
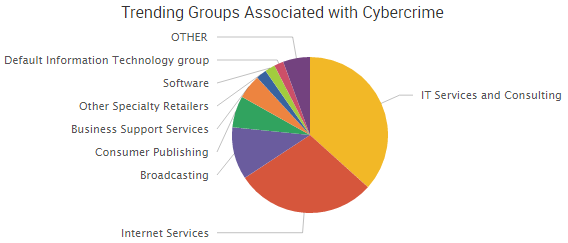
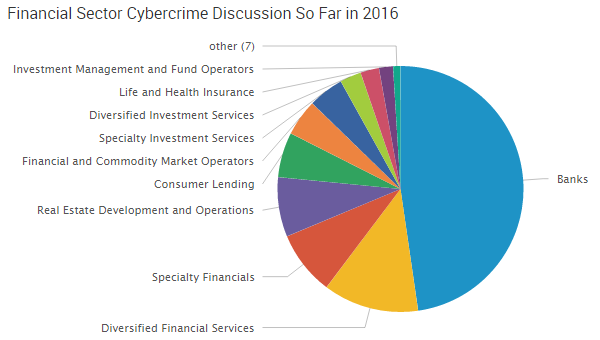
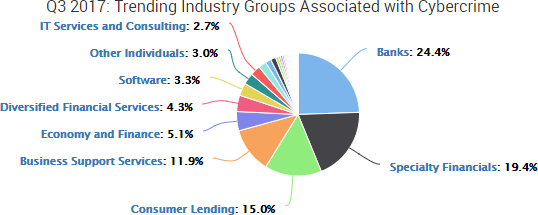
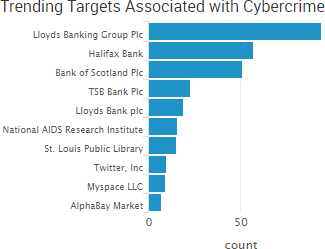
- Banks remained as the top trending group associated with cybercrime in the financials sector, accounting for nearly one quarter (24.4%) of the negative cyber events collected by SurfWatch Labs; however, that percentage was down from 38.1% in the first half 2017 and 35.8% across all of 2016.
- That drop was largely attributed to increased activity in the specialty financials group, which saw its percentage of threat intelligence jump from 7.4% in the first half of 2017 to 19.4% in Q3 as malicious actors increasingly targeted cryptocurrency platforms.
- Payment cards were the dark web target category to see the most significant increase, accounting for 14.6% of the financials sector’s dark web threat intelligence – a rise from 7.1% in the first half of 2017.
Malicious Actors Increasingly Targeting Cryptocurrency
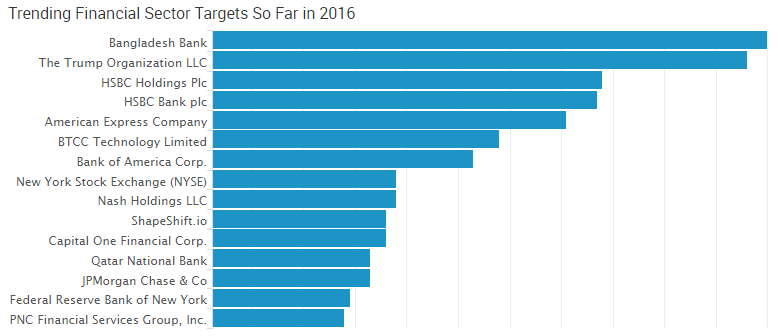
Cybercrime incidents related to the banking group remained the most widespread in SurfWatch Labs’ Q3 threat intelligence data. However, when excluding our dark web data, many of the most noteable cyber-attacks – including all five of the top trending incidents for the period – occurred at cryptocurrency organizations in the specialty financials group.
Several of the top trending cyber-attacks in Q3 revolved around the hijacking of Ethereum Initial Coin Offerings (ICO) in order to steal cryptocurrency. Notable attacks include:
-
- In July, Coindash said that an actor gained access to its website during the company’s ICO and changed the text on the site to a fraudulent Ether wallet address – resulting in $10 million worth of Ether being stolen from investors.
- Veritaseum also reported in July that it had $8.4 million worth of tokens stolen during its ICO as a result of a “very sophisticated” attack, which may have involved at least one corporate partner dropping the ball, according to the company’s founder.
- In August, Enigma Catalyst said that investors were scammed out of approximately $500,000 of Ether when malicious actors hijacked the company’s website, mailing lists, and Slack accounts and subsequently offered a fake pre-sale to investors ahead of the company’s upcoming ICO.
In addition, there were a variety of other cryptocurrency-related attacks during the period. For example, a bug was found in the multi-signature wallet code used as part of Parity Wallet software, which led to wallets being exploited and reports of approximately $34 million worth of Ether being stolen before white hat hackers intervened to prevent an additional $85 million in theft. In addition, a malicious actor was also able to trick the hosting provider of the open source Classic Ether Wallet into hijacking the Classic Ether Wallet domain, resulting in potential theft as transactions were made on the site.
As cryptocurrencies continue to gain legitimacy and value, it is likely that malicious actors will continue to shift towards targeting them in both the near and long term. For example, one group is tracking over 150 active Ethereum scams heading into the fourth quarter of the year. Exploiting the popularity of cryptocurrencies has proven to be highly profitable for both cybercriminals and state actors, such as North Korea.
Fraud Activity Increases on the Dark Web
SurfWatch Labs also observed an increase in the amount of fraud-related activity in Q3, with fraud accounting for 43.6% of financials dark web threat intelligence – a significant jump from previous periods. In the first half of 2017, fraud accounted for 24.4% of collected dark web intelligence, and during 2016 it accounted for 24%.
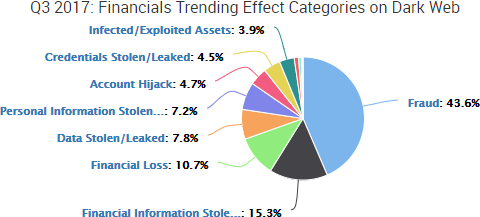
Digging deeper into the data, it is clear that point-of-sale (POS) and other payment card breaches helped to drive a significant portion of fraud activity in Q3. In the first half of 2017, the target tag of “payment cards” appeared in only 8.3% of the dark web threat intelligence collected by SurfWatch Labs. In Q3 that number rose to 14.5%.
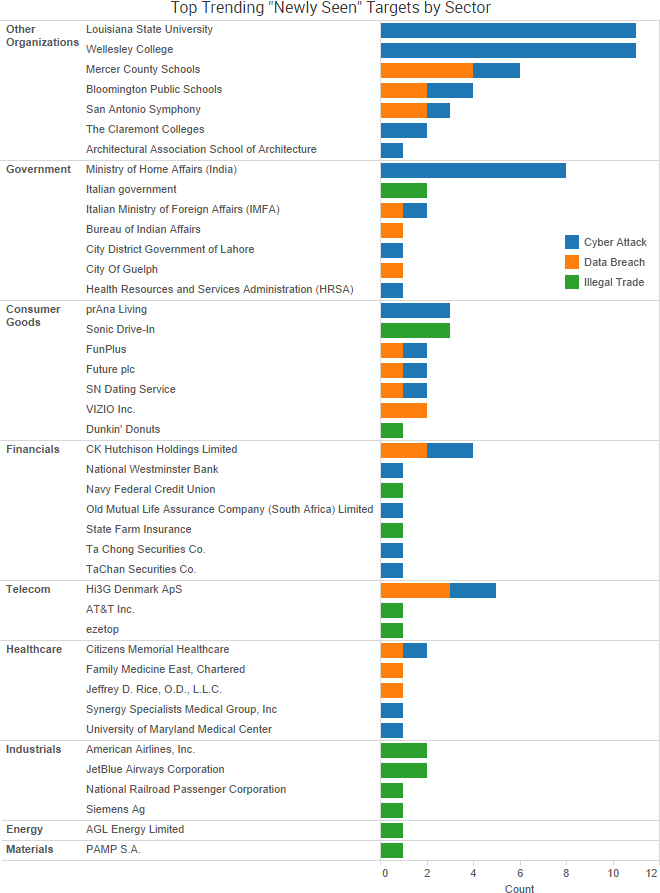
Some of the notable payment card breaches announced during Q3 include:
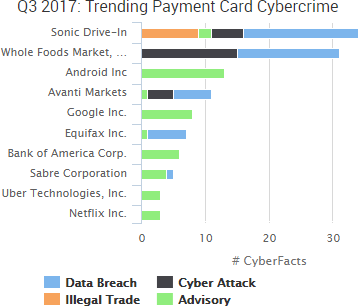
- The fast food chain Sonic has been tied to at least a portion of five million fresh payment cards being sold on a cybercriminal market.
- Whole Foods announced a POS breach involving its taprooms and restaurants.
- Avanti announced a POS breach affecting an undisclosed number of the company’s self-serve snack kiosks.
- Equifax’s massive breach included more than 200,000 payment cards.
- B&B Theaters announced it was investigating a payment card breach that may date all the way back to 2015.
- Sabre announced a breach affecting its SynXis Central Reservations system back in May, and affected hotels continued to issue breach notification letters throughout Q3.
- Third-party vendor Aptos continues to be tied to payment card breaches at online retailers.
Other payment card breach notifications and investigations have continued to be announced in the days since Q3 ended, including a POS breach at Hyatt Hotels and Irish retailer Musgrave warning SuperValu, Centra, and Mace customers to be on the lookout for fraud. In addition, Flexshopper announced it exposed payment card information, and Tommie Cooper and Cricut announced they discovered malware on their website checkout pages.
Numerous organizations also warned of payment cards phishing scams during the period – including Netflix, Uber, E-ZPass, Newcastle University, and more. A number of other data breaches and leaks involved partial payment card information.
Conclusion
The financials sector continues to be the target of a wide range of attacks due to the nature of the data organizations hold and the services they provide. As we noted in our Fraud and the Dark Web whitepaper, the number of avenues through which malicious actors can carry out fraud has increased along with the number of digital accounts tied to financial information. However, Q3 saw an increase in more traditional payment card fraud activity on the dark web – likely resulting from several large one-off POS breaches, as well as issues at vendors that have spread through the supply chain to affect both in-person and online purchases.
On the flip side, the number of cryptocurrency related breaches, particularly those tied to Ethereum, have highlighted a shift that may have legs – particularly since there is less regulation and, in some cases, less security to circumvent in order to pull off multi-million dollar heists. For example, it was reported that at least one Slack account with administrative privileges at Enigma used a previously leaked password and didn’t require two-factor authentication. Likewise, the incident involving Classic Ether Wallet began by simply socially engineering a third party over the phone by impersonating the site’s owner. Malicious actors are quick to copy the successful techniques of their peers, and we will likely see similar attempts against cryptocurrency organizations in the future.


 In addition to Yahoo, the past few weeks have seen several new regulatory announcements and fines related to data breaches.
In addition to Yahoo, the past few weeks have seen several new regulatory announcements and fines related to data breaches.
 The Guardian
The Guardian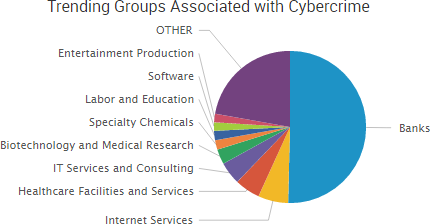
 The fallout over two massive data breaches at Yahoo continued this past week as it was reported that the Securities and Exchange Commission (SEC) opened an investigation into the timeline of Yahoo’s data breach disclosure and that the sale of Yahoo’s main web operations to Verizon has been delayed until the next quarter.
The fallout over two massive data breaches at Yahoo continued this past week as it was reported that the Securities and Exchange Commission (SEC) opened an investigation into the timeline of Yahoo’s data breach disclosure and that the sale of Yahoo’s main web operations to Verizon has been delayed until the next quarter.
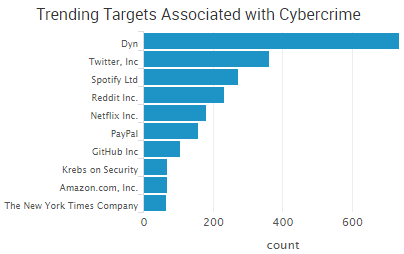 According to some reports, the DDoS attack may have surpassed one terabyte per second of traffic; however, the
According to some reports, the DDoS attack may have surpassed one terabyte per second of traffic; however, the