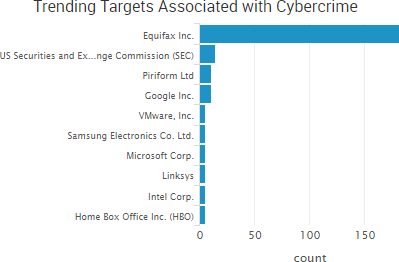
The U.S. Securities and Exchange Commission (SEC) was the week’s top trending new cybercrime target following the announcement that a data breach compromised sensitive data that may have “provided the basis for illicit gain through trading.” SEC chairman Jay Clayton said the commission learned last month that an incident “previously detected” in 2016 may have led to the illicit trading.
“Specifically, a software vulnerability in the test filing component of our EDGAR system, which was patched promptly after discovery, was exploited and resulted in access to nonpublic information,” Clayton said in a statement.
EDGAR — which is an acronym for electronic data gathering, analysis, and retrieval — contains millions of filings from companies. The investigation is ongoing, but it is likely that any insider trading due to the breach would have occurred between the period when company filings were made and when those filings were released to the public. The SEC breach echoes, on a smaller scale, the insider trading scheme for which a Ukrainian hacker was sentenced to prison earlier this year. That scheme revolved around the theft of 150,000 news releases from Business Wire, Marketwired, and PR Newswire between February 2010 and August 2015, which led to more than $100 million in illegal profits.
Reuters said it had viewed a confidential report stating that the U.S. Department of Homeland Security detected five “critical” weaknesses on the SEC’s computers as of January 23. In addition, the Government Accountability Office warned in July that the SEC was “at unnecessary risk of compromise” because of deficiencies in its information systems. Reuters also reported that new SEC reporting rules start to come into effect in December that require funds to confidentially file monthly, rather than quarterly, portfolio holdings with the SEC. The breach has unnerved investor groups such as the Investment Company Institute, which wants the SEC to answer cybersecurity concerns before the SEC begins collecting additional sensitive data.
Other trending cybercrime events from the week include:
- TheDarkOverlord threatens violence: Flathead County in Montana closed 30 schools for several days following a breach and ransom letter that claimed to come from TheDarkOverlord and hinted at physical violence, as well as threats against individual families that leveraged the school’s electronic directory. Databreaches.net wrote that “the Flathead case is not the first case where TheDarkOverlord has contacted its victims by phone or SMS to threaten them or deliver obscenity-laden messages.”
- Organizations expose more data: Researchers discovered an Amazon AWS S3 bucket belonging to Viacom that contained “a vast array of internal access credentials and critical data that could be used to cause immense harm to the multinational corporation’s business operations.” Researchers discovered an Amazon AWS S3 bucket with more than half a million records belonging to the automobile tracking company SVR Tracking. The Office of the Australian Information Commissioner is investigating the exposure of the financial information of customers of Amazing Rentals. The British supermarket chain Iceland exposed customer information on its home delivery confirmation sheets, which also contained an IP address that led to a insecure login portal for Iceland’s scheduling system. Premier Medical Associates said that 900 patients that submitted information via the “Contact Us” portion of its website had that data compromised due to search engines retrieving the submissions.
- New data breaches: OurMine gained access to Vevo’s media storage servers and leaked 3.12TB of company data. Bulletproof 360 is notifying customers that their payment information may have been compromised due to the discovery of unauthorized code on its website’s checkout page. TD Ameritrade said “unauthorized code” led to the breach of customer information. LiteBit is notifying users that their personal information was accessed in an attack that targeted a supplier and a LiteBit server. Cornerstone Business and Management Solutions said that it discovered an unauthorized account on a server and that the data of Certified Medical Supplies patients was compromised. Irish National Teachers’ Organization said that more than 30,000 teachers had their personal information compromised due to hackers gaining access to its online learning portal. TRUEbenefits, ABB, Inc., Morehead Memorial Hospital in North Carolina, and AU Medical Center all announced breaches due to compromised employee email accounts.
- Other notable incidents: Montgomery County in Alabama said that a ransomware infection locked up computer systems and disrupted some county services. PeaceHealth Southwest Medical Center is notifying 1,969 patients that their protected health information was unnecessarily accessed by an employee. A Georgia man was found guilty of inserting malicious code known as a “logic bomb” into a national-level computer program responsible for handling pay and personnel actions for nearly 200,000 U.S. Army reservists. An Arizona man was sentenced to four years of federal probation for making changes to a company website that prevented the company’s employees from using their email accounts, redirecting the company’s homepage to a blank page, demanding $10,000 to return everything to normal, and then redirecting the company’s homepage to a pornographic website when it refused to pay the ransom.
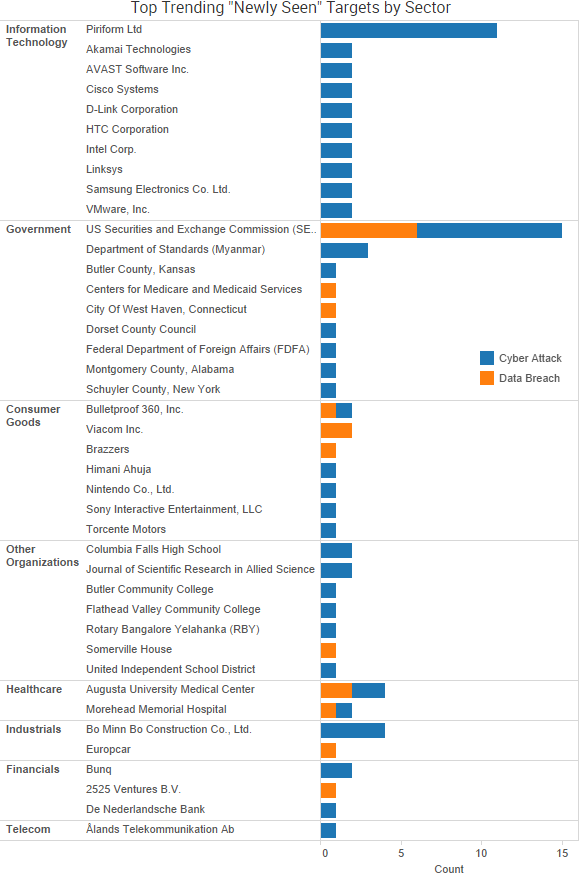
SurfWatch Labs collected data on many different companies tied to cybercrime over the past week. Some of those “newly seen” targets, meaning they either appeared in SurfWatch Labs’ data for the first time or else reappeared after being absent for several weeks, are shown in the chart below.
Cyber Risk Trends From the Past Week
 Last week the developer of CCleaner announced that approximately 2.27 million users of CCleaner downloaded a legitimately signed version of the utility containing malicious code. Shortly thereafter, it was reported that the spreading of a backdoored version of CCleaner appears to have been an espionage campaign designed to gain access to the networks of at least 18 tech firms.
Last week the developer of CCleaner announced that approximately 2.27 million users of CCleaner downloaded a legitimately signed version of the utility containing malicious code. Shortly thereafter, it was reported that the spreading of a backdoored version of CCleaner appears to have been an espionage campaign designed to gain access to the networks of at least 18 tech firms.
The malicious version of CCleaner was available on the site from August 15 to September 12, said Piriform, which was recently acquired by Avast, and affected customers with the 32-bit version of the v5.33.6162 of CCleaner and the v1.07.3191 of CCleaner Cloud. The compromised code could have resulted in “the transmission of non-sensitive data (computer name, IP address, list of installed software, list of active software, list of network adapters) to a 3rd party computer server in the USA.”
Researchers found evidence that the actors attempted to filter their collection of compromised victim machines to find computers inside the networks of tech firms, such as Intel, Google, Microsoft, Akamai, Samsung, Sony, VMware, HTC, Linksys, D-Link, Cisco, and more. In about half of the cases, the actors behind the attack successfully compromised a machine within the company’s network and used that to install another piece of malware likely intended for industrial espionage. The researchers also noted that the list of targets discovered was likely modified throughout the month-long campaign, so there may be additional companies that were targeted besides the 18 that were identified.
“These findings also support and reinforce our previous recommendation that those impacted by this supply chain attack should not simply remove the affected version of CCleaner or update to the latest version, but should restore from backups or reimage systems to ensure that they completely remove not only the backdoored version of CCleaner but also any other malware that may be resident on the system,” Cisco researchers wrote.


