Ukrainian power utility Ukrenergo was back in the news as the top trending cybercrime target after researchers analyzed new samples of a destructive malware, dubbed “Win32/Industroyer,” which they said was likely used in the December 2016 attack against the Ukrainian power grid.

“Industroyer is a particularly dangerous threat, since it is capable of controlling electricity substation switches and circuit breakers directly,” ESET researchers wrote. “To do so, it uses industrial communication protocols used worldwide in power supply infrastructure, transportation control systems, and other critical infrastructure systems (such as water and gas).”
The Industroyer malware uses four payload components designed to gain control of switches and circuit breakers, with each component targeting a particular communication protocol: IEC 60870-5-101, IEC 60870-5-104, IEC 61850, and OLE for Process Control Data Access (OPC DA). The malware is notable as it “is capable of doing significant harm to electric power systems and could also be refitted to target other types of critical infrastructure.”
Hackers may have hidden in Ukrenergo’s IT network undetected for six months before carrying out their December 2016 attack, which led to a power blackout in Kiev that lasted a little over an hour. Although it’s not confirmed, it is “highly probable” that Industroyer was used in that incident. The Ukrenergo attack occurred a year after a similar attack against Prykarpattyaoblenergo, which caused approximately 230,000 people to lose power. Researchers have warned that both of those incidents in Ukraine could be tests for potential attacks against Western countries’ critical infrastructure facilities in the future.

Other trending cybercrime events from the week include:
- FIN10 targeted mining companies and casinos: A financially-motivated hacking group known as FIN10 spent at least three years infiltrating computers at several unnamed Canadian mining companies and casinos, stealing sensitive data, and then holding it for ransom. According to researchers, the attacks targeted sensitive files such as corporate records, private communications, and customer information, and the ransom demands ranged between 100 and 500 bitcoin. The hackers were also able to essentially shut off the production systems of some mines or casinos that did not comply, making them unable to operate for a period of time.
- Updates on previously disclosed attacks: The attackers behind the 2015 attack against TV5Monde conducted reconnaissance inside the TV5Monde network for three months before launching a sabotage operation that knocked multiple channels offline and compromised multiple social media accounts. France’s national cybersecurity agency said that the attackers used a compromised third-party account that allowed them to connect to the TV5Monde VPN and that once they were inside the network they used one of two camera-control servers as a beachhead for privilege escalation. The agency also noted that the attackers were able to create their own admin-level account in Active Directory and used the IT department’s wiki to gain information. GameStop is notifying an undisclosed number of online customers that their payment card details were stolen between August 10, 2016 and February 9, 2017. The breach was acknowledged by GameStop in April, but the company only recently began notifying affected customers. Cowboys Casino in Alberta said that data stolen from a breach last year has been posted online and that the hackers are threatening to post more data next week. WikiLeaks’ latest dump of CIA documents is CherryBlossum, a project that is focused on compromising wireless networking device.
- Universities targeted: Southern Oregon University said it sent $1.9 million to a malicious actor impersonating Andersen Construction, a contractor that is working on the McNeal Pavilion and Student Recreation Center construction project. University College London said that a major ransomware attack occurred on June 14 and disrupted access to a number of users’ personal and shared drives for several days after UCL users visited a compromised website. Ulster University in Northern Ireland was infected with ransomware that affected a “significant number of file shares” due to a “zero day attack.” The initial attack occurred on June 14, and the university said it believes they are will be in a position to restore the file share service by late morning on June 19.
- Other notable incidents: A database containing the personal information of 6 million users of online survey site CashCrate was stolen by hackers due to an apparent compromise of third-party forum software. A developer at Tata Consultancy Service in India posted the source code and internal documents for a number of unnamed financial institutions to a public GitHub repository. Italy’s data protection authority said that Wind Tre, the country’s biggest mobile operator in terms of mobile SIMs, must notify customers of a March 20 data breach that affected 5,118 customers. A hacker pleaded guilty to the 2014 theft of hundreds of user accounts from a U.S. military communications system, an intrusion that the Department of Defense said cost $628,000 to fix.
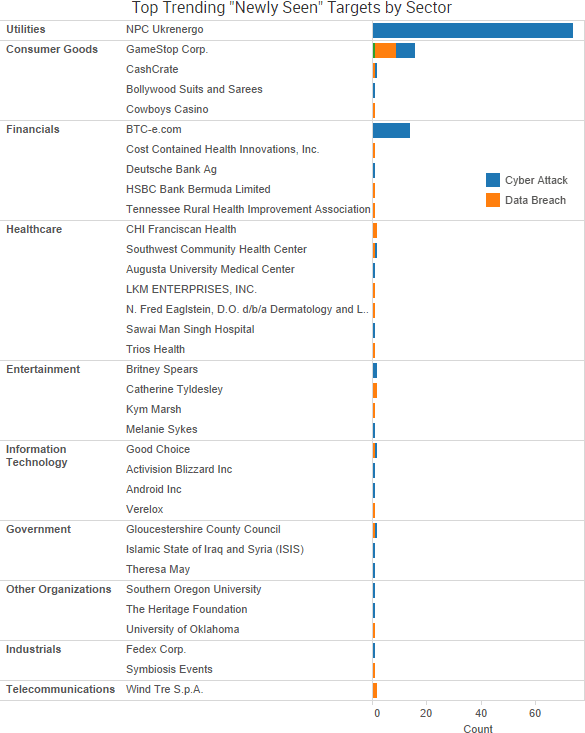
SurfWatch Labs collected data on many different companies tied to cybercrime over the past week. Some of those “newly seen” targets, meaning they either appeared in SurfWatch Labs’ data for the first time or else reappeared after being absent for several weeks, are shown in the chart below.
Cyber Risk Trends From the Past Week
 New York’s attorney general Eric Schneiderman announced last Thursday that CoPilot Provider Support Services must pay $130,000 in penalties as well as reform its legal compliance program over violations related to delayed notification of a breach.
New York’s attorney general Eric Schneiderman announced last Thursday that CoPilot Provider Support Services must pay $130,000 in penalties as well as reform its legal compliance program over violations related to delayed notification of a breach.
According to the attorney general, an October 2015 data breach of CoPilot’s website administration interface, PHPMyAdmin, allowed an unauthorized user to download reimbursement-related records for 221,178 patients, including their names, genders, dates of birth, addresses, phone numbers, and medical insurance card information. However, CoPilot did not begin formally notifying affected consumers until January 2017, more than a year after the incident occurred — an “unacceptable” violation of New York law.
“Although CoPilot asserted that the delay in providing notice was due to an ongoing investigation by law enforcement, the FBI never determined that consumer notification would compromise the investigation, and never instructed CoPilot to delay victim notifications,” New York’s attorney general wrote. “General Business Law § 899-aa requires companies to provide notice of a breach as soon as possible, and a company cannot presume delayed notification is warranted just because a law enforcement agency is investigating.”
In January, the U.S. Department of Health and Human Services, Office for Civil Rights (OCR) issued a $475,000 fine to Presence Health for similar reasons. OCR said that it was the agency’s first HIPAA settlement based on the untimely reporting of a breach of unsecured protected health information and that the settlement amount “balanced the need to emphasize the importance of timely breach reporting with the desire not to disincentive breach reporting altogether.”
That regulatory scrutiny may get more intense with the enforcement of the EU’s General Data Protection Regulation (GDPR) next year. The GDPR requires companies notify the appropriate authorities of a breach within 72 hours of discovery if that company collects, stores, or processes personal data for people residing in the EU. As SearchSecurity noted last month, that could force a change for the better when it comes to prompt breach notification by companies since the monetary penalties associated with violating the GDPR are much harsher than the current regulations.
