The San Francisco Municipal Transportation Agency (SFMTA) is continuing to deal with the fallout from a Friday ransomware attack that affected 900 office computers and led to passengers getting free rides as ticket machines were taken offline. The agency has since restored systems from a backup, and fares have been running as normal since Sunday; however, the actor behind the attack is still threatening to release 30GB of data if the 100 bitcoin ransom ($75,000) is not paid by tomorrow.
The actor, going by the name Andy Saolis, has refused to provide media outlets with a sample of the stolen data in order to verify the alleged theft, and SFMTA said that its ongoing investigation has not discovered that any data exfiltration took place.
“[N]o data was accessed from any of our servers,” the agency said in a statement. “The SFMTA has never considered paying the ransom. We have an information technology team in place that can restore our systems, and that is what they are doing.”
Many Organizations Choose to Pay
While SFMTA has decided not to pay the ransom, other organizations targeted by the same threat actor have been successfully extorted. A security researcher who gained access to an email account used by Andy Saolis said that the hacker had extorted at least $140,000 in bitcoins from victim organizations over the past few months, including 63 bitcoins (around $45,000) from a U.S.-based manufacturing firm. The emails also show that this past Sunday another company, China Construction of America Inc., paid 24 Bitcoins (around $17,500) to decrypt 60 servers infected with the same strain of ransomware, known as HDDCryptor or Mamba.
In addition to the attacks described above, SurfWatch Labs has collected, evaluated and analyzed data pertaining to dozens of other targets associated with extortion over the past month.

The top trending ransomware story over the past 30 days is the newly discovered attack vector known as ImageGate, which is infecting numerous users with Locky ransomware via Facebook and LinkedIn by exploiting a misconfiguration that forces victims to download a malicious image file. It’s unclear how many of those victims have paid the ransom, but a variety of other organizations have publicly confirmed making ransom payments recently:
- The Lansing Board of Water & Light recently acknowledged it paid a $25,000 ransom after an employee opened an attachment that led to a ransomware.
- A $28,000 ransom was paid after an infection locked up several government systems in Madison County, Indiana and the county’s insurance carrier advised payment.
- The New Jersey Spine Center paid an undisclosed amount after CryptoWall encrypted all electronic medical records and the most recent system backup, as well as disabled the phone system.
- Cloud service provider VESK said that it paid £18,600 after being infected with a strain of the Samas DR ransomware
Government Agencies Continue to Warn of Threat
Despite the many public incidents of late, the vast majority of ransomware attacks are believed to go unreported. That’s why in September the FBI urged victims to report infections regardless of the outcome. The FBI also warned of cybercriminals shifting tactics to target servers in order to receive larger ransoms.
“Actors engaging in this targeting strategy are also charging ransoms based on the number of host (or servers) infected,” the FBI warned. “This recent technique of targeting host servers and systems could translate into victims paying more to get their decryption keys, a prolonged recovery time, and the possibility that victims will not obtain full decryption of their files.”

In November, the Federal Trade Commission also warned organizations that it may investigate certain ransomware incidents.
“[I]n some cases, a business’ inability to maintain its day-to-day operations during a ransomware attack could deny people critical access to services like health care in the event of an emergency,” wrote Ben Rossen, an attorney at the FTC. “Thus, a company’s failure to update its systems and patch vulnerabilities known to be exploited by ransomware could violate Section 5 of the FTC Act.”
The Department of Health and Human Services issued a similar statement over the summer, warning that in most cases a ransomware infection would qualify as a reportable “breach”:
The presence of ransomware (or any malware) on a covered entity’s or business associate’s computer systems is a security incident under the HIPAA Security Rule. …
When electronic protected health information (ePHI) is encrypted as the result of a ransomware attack, a breach has occurred because the ePHI encrypted by the ransomware was acquired (i.e., unauthorized individuals have taken possession or control of the information), and thus is a “disclosure” not permitted under the HIPAA Privacy Rule.
As the FBI noted, new ransomware variants are emerging regularly and global ransomware infections continue to grow. Organizations need to ensure they have a plan in place to deal with this threat.
SurfWatch Labs’ Recommend Courses of Action
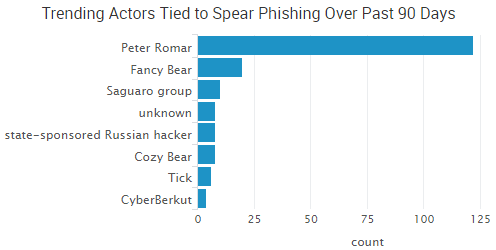
A large percentage of ransomware is spread via social engineering techniques; therefore, SurfWatch Labs advises customers that user education around tactics such as spear phishing is the best method to prevent these kinds of attacks. In addition, having data that is backed up and can be restored is often the quickest and cheapest way to get operations back up and running. Organizations should make regular backups that are not stored on local machines or connected through network shares.
Other ransomware prevention tips include:
- Antimalware software configured to scan all email attachments will help catch most malicious attachments. All settings that allow the documents to download and open directly should also be disabled.
- General users should be restricted from administrator-level permissions on their local machines, unless specifically required. Limiting this privilege could lessen the impact of ransomware.
- The ‘vssadmin’ utility should be removed unless it is justifiably required to be on the system. This will not stop the encryption from occurring, but could assist with recovering key files from a machine that has been affected if the system’s shadow copy files are left intact.
- It’s recommended that Remote Desktop Protocol (RDP) be disabled as this can exploited by certain ransomware types.
- Since HDDCryptor creates a suspicious set of files, using Host Intrusion Prevention (HIPS) software can help detect this activity.
- All Macros in MS Office programs should be disabled to ensure no accidental activation of an infected document. Users should be made aware not to activate macros on documents that are unverified.
- When possible, segmenting networks by role and criticality may prevent the spread of the malware itself or limit the extent of the network is impacted when a device is compromised.
- Keep operating systems, software, and antivirus protections patched and up to date.


 The information compromised in the Adult Friend Finder hack dates back 20 years, according to
The information compromised in the Adult Friend Finder hack dates back 20 years, according to 










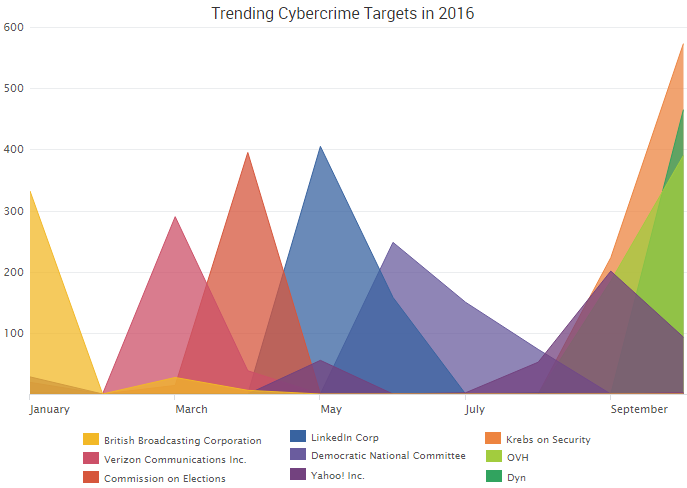

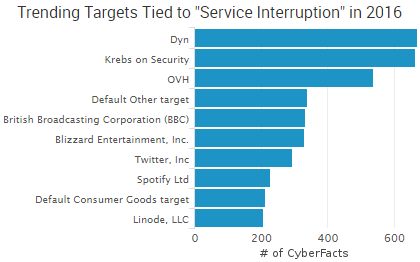
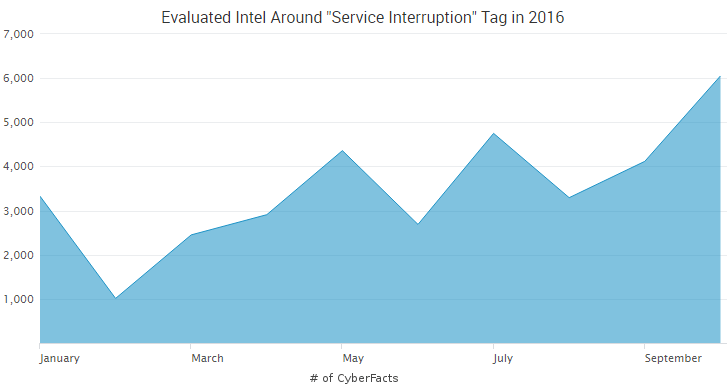
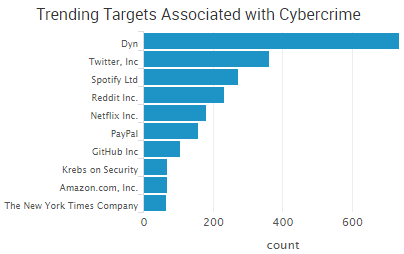 According to some reports, the DDoS attack may have surpassed one terabyte per second of traffic; however, the
According to some reports, the DDoS attack may have surpassed one terabyte per second of traffic; however, the 


 It was also recently announced that
It was also recently announced that 


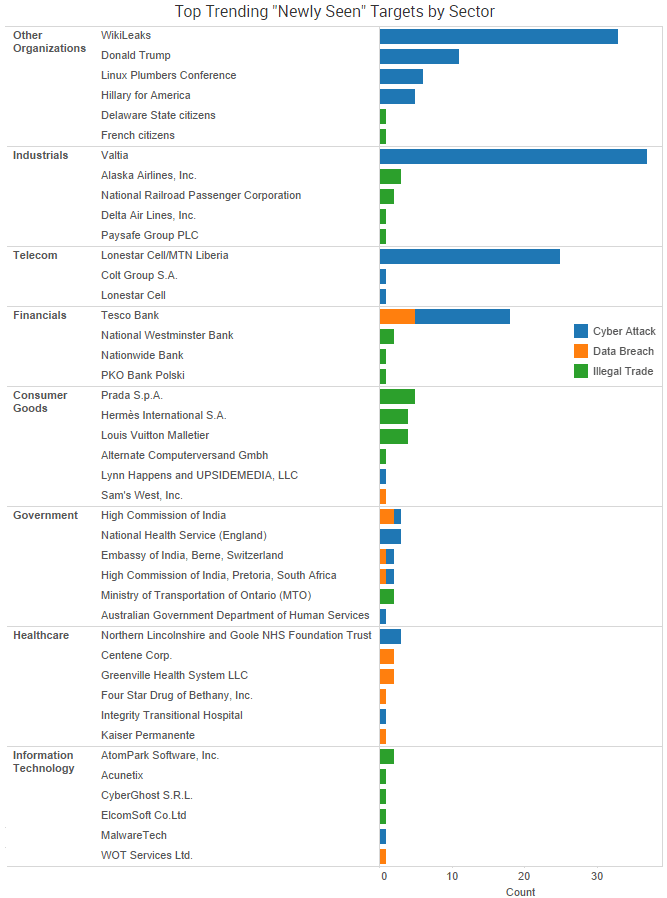
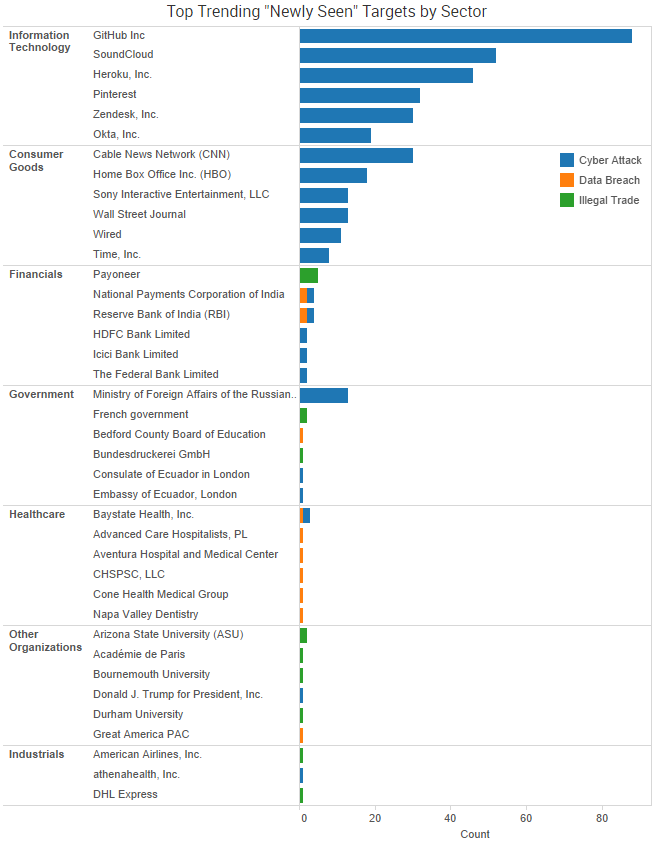
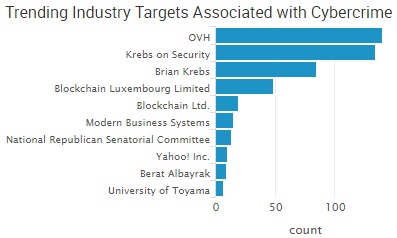
 On Tuesday, University of Central Florida police announced they were able to tie a recent surge in fraud reports to malware on the systems of
On Tuesday, University of Central Florida police announced they were able to tie a recent surge in fraud reports to malware on the systems of