A series of distributed denial-of-service (DDoS) attacks against financial institutions led to customers of Lloyds Banking Group experiencing intermittent outages over a 48-hour period and was the top trending cybercrime event over the past week.
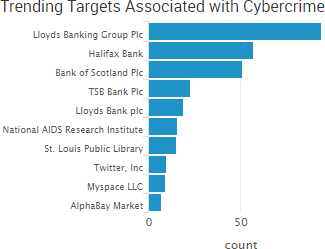 The Guardian reported that the attacks hit Lloyds, Halifax and Bank of Scotland from January 11 to January 13. IBTimes reported that other unnamed lenders were targeted, but experienced no down time. Motherboard spoke to a hacker who claimed to be behind the attack and allegedly tried to ransom Lloyds over the incident. However, Lloyds issued a statement saying it was able to provide normal service for “the vast majority” of customers and that “only a small number” experienced any issues during the attack.
The Guardian reported that the attacks hit Lloyds, Halifax and Bank of Scotland from January 11 to January 13. IBTimes reported that other unnamed lenders were targeted, but experienced no down time. Motherboard spoke to a hacker who claimed to be behind the attack and allegedly tried to ransom Lloyds over the incident. However, Lloyds issued a statement saying it was able to provide normal service for “the vast majority” of customers and that “only a small number” experienced any issues during the attack.
In other DDoS news, the ticketing systems for the Sundance Film Festival were taken offline due to a cyber-attack on January 21. “We have been subject to a cyberattack that has shut down our box office,” the festival tweeted. “Our artist’s voices will be heard and the show will go on.” According to The Hollywood Reporter, “although the festival was able to get its ticketing systems back online within an hour of the Saturday breach, multiple other denial-of-service (DDoS) attacks on Sundance’s IT infrastructure followed.”
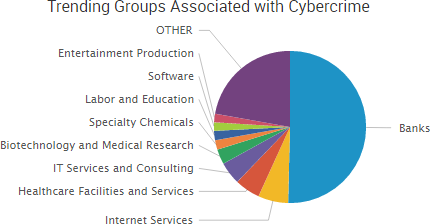
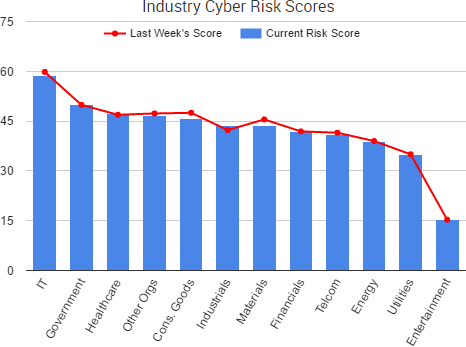
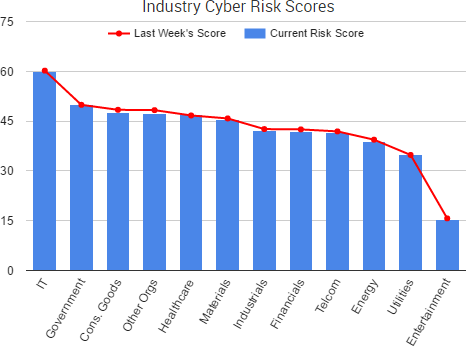
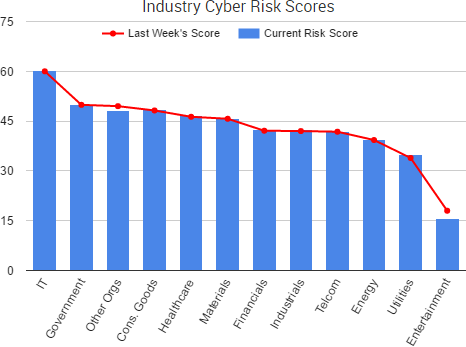
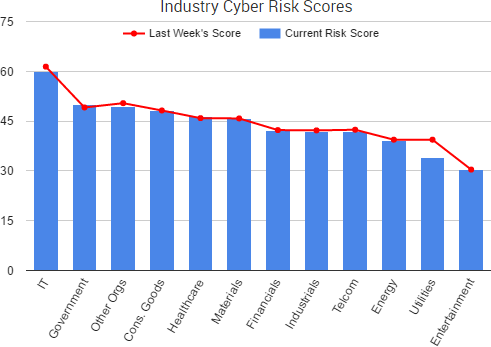
Finally, the Korea Internet & Security Agency recently issued a report echoing concerns shared by other security professionals, including SurfWatch Labs Adam Meyer: expect DDoS attacks leveraging Internet-of-Things devices to rise in 2017. South Korea has recently faced political turmoil, and in December the country’s Constitutional Court began its first hearings on the impeachment of President Park Geun-hye. The agency report predicted that DDoS attacks may occur against key government agencies and social infrastructure-related facilities with the goal of stirring the political and social instability brought on by the impeachment proceedings and potential upcoming election. According to SurfWatch Labs’ data, government was the third highest trending sector related to DDoS attacks in 2016, behind only information technology and consumer goods.
Other trending cybercrime events from the week include:
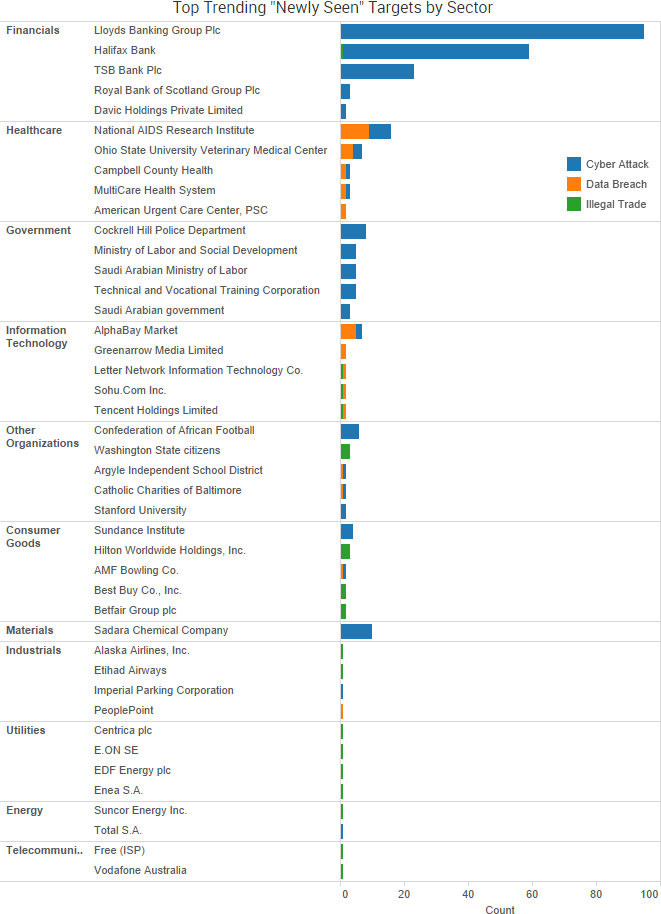
- Another year of W-2 breaches begins: Approximately 1,400 Campbell County Health employees had their W-2 information stolen when an employee fell for a phishing email impersonating a hospital executive. Eight Missouri school districts were targeted with identical phishing messages impersonating the superintendent and requesting employee W-2 information, and an employee at the Odessa School District fell for the scam and forwarded the information. The Argyle Independent School District in Texas and the Tipton County School District also reported breaches due to similar phishing emails.
- Media outlets hit with political attacks: The Twitter accounts of BBC Northampton and The New York Times video were both hijacked and used to spread fake messages saying that President Donald Trump was injured in the arm by gunfire at his inauguration and that Russia was planning to attack the U.S. with missiles. Crescent Hill Radio WCHQ said its FM feed was hacked and a song titled “Fuck Donald Trump” was played on repeat for 15 minutes before the station could shut down the broadcast.
- Exposed databases reveal sensitive data: Security researchers have found nearly 400,000 audio recordings belonging to VICI Marketing exposed to the Internet, and as many as 17,649 of those recordings include customer payment card numbers and private customer information. The other 375,368 audio recordings are “cold calls,” some of which contain personal information. A misconfigured database used by The Candid Board, a subscription website dedicated to images and video of women who appear unaware they are being recorded, led to the leak more than 178,000 members’ information. The source also said that he or she is in possession of “a large chunk of data from multiple boards operated by this group,” which IBTimes explained was in reference to another leaked database holding tens of thousands of records from a website called NonNudeGirls.
- Arrests and charges: A former employee of First Niagara call center admitted to using his position to steal callers’ personal information and then using that information to transfer $15,492.59 from customer accounts to his own. An IT worker employed by the New York Police Department accessed personnel files of police officers and then attempted to sell that information to an undercover informant. A 32-year old Russian programmer suspected of developing the NeverQuest banking Trojan was arrested in Barcelona, according to Spanish authorities.
- Other cybercrime announcements: A hacker gained access to a server for the National Aids Research Institute in India and was able to access an archive containing the results of dozens of HIV tests. Malware was found on computers at 21 locations of Bowlmor AMF, the world’s largest bowling center operator, leading to a point-of-sale breach. Cockrell Hill Police Department in Texas lost some digital videos and documents dating back to 2009 after ransomware encrypted the departments files and those encrypted files were then saved to the automatic backup system. Other breach announcements include the South Washington County School district in Minnesota, MultiCare Health System, Ohio State Veterinary Medical Center at Dublin, Catholic Charities of Baltimore, and Wisconsin Democratic Party websites.
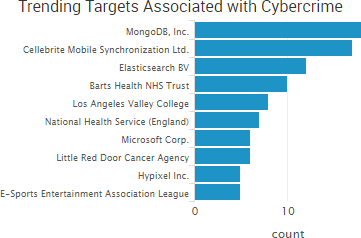
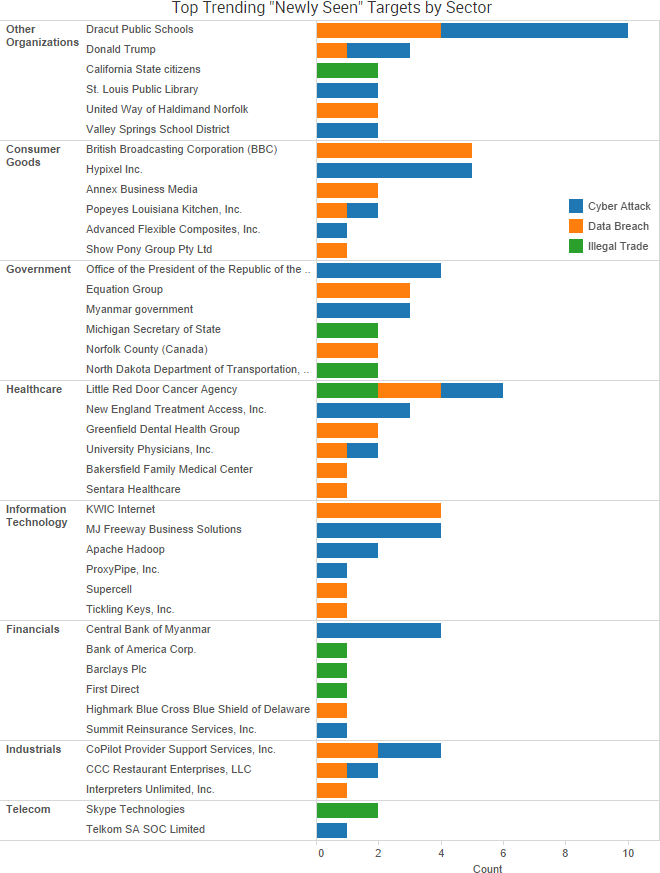
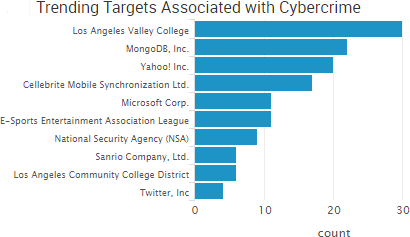
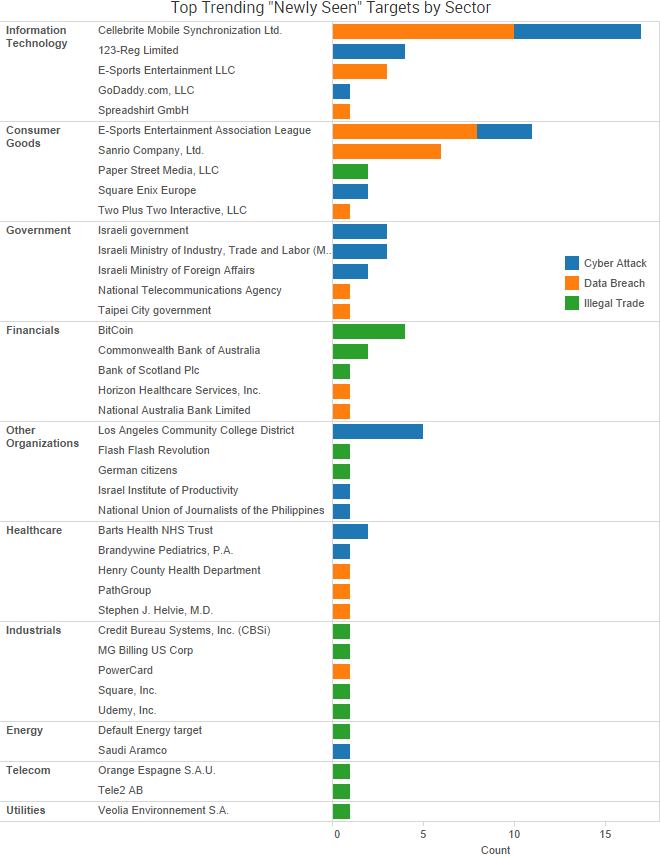
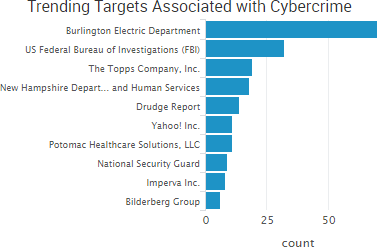
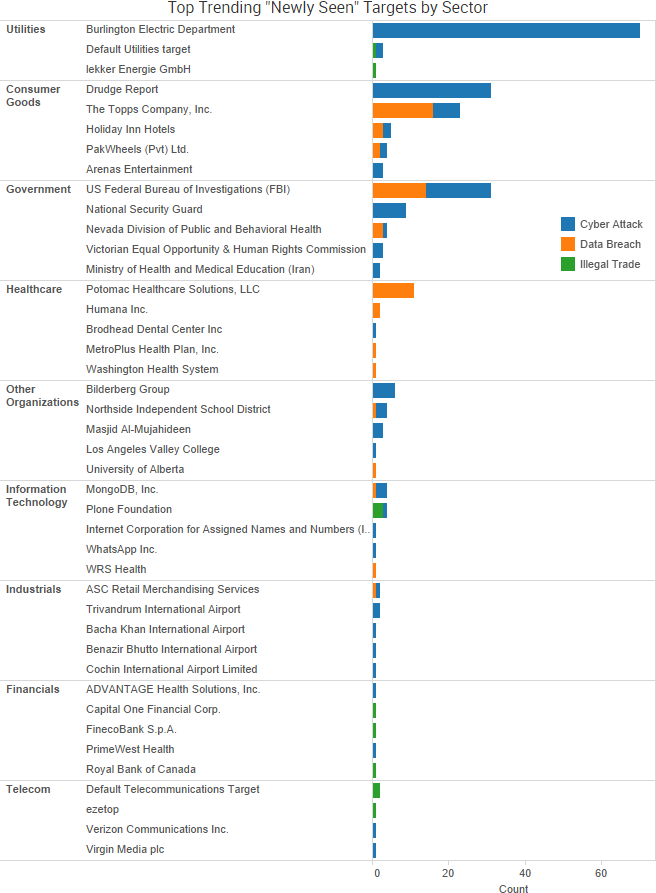
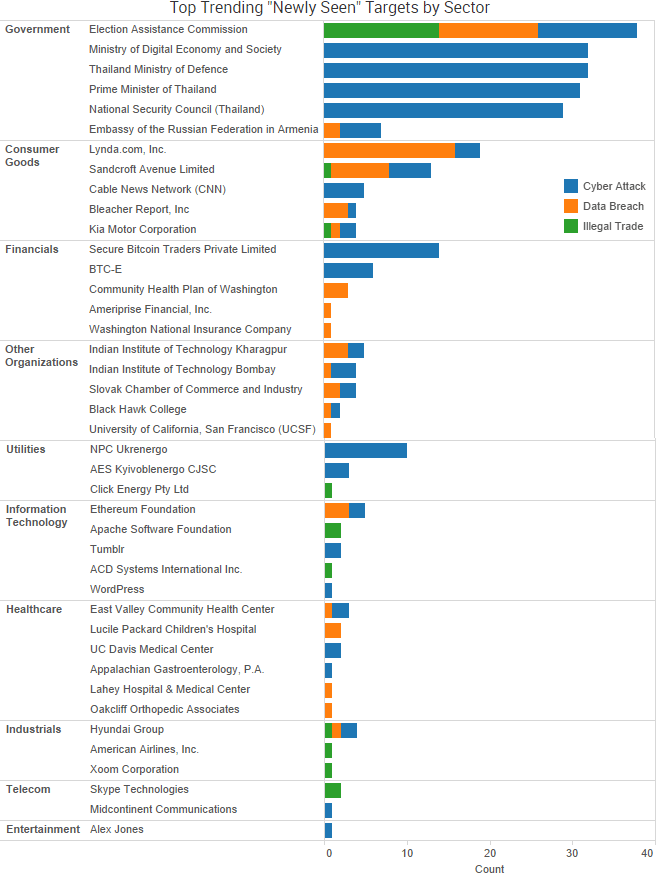
SurfWatch Labs collected data on many different companies tied to cybercrime over the past week. Some of those “newly seen” targets, meaning they either appeared in SurfWatch Labs’ data for the first time or else reappeared after being absent for several weeks, are shown in the chart below.
Cyber Risk Trends From the Past Week
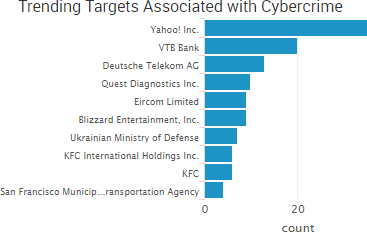
 The fallout over two massive data breaches at Yahoo continued this past week as it was reported that the Securities and Exchange Commission (SEC) opened an investigation into the timeline of Yahoo’s data breach disclosure and that the sale of Yahoo’s main web operations to Verizon has been delayed until the next quarter.
The fallout over two massive data breaches at Yahoo continued this past week as it was reported that the Securities and Exchange Commission (SEC) opened an investigation into the timeline of Yahoo’s data breach disclosure and that the sale of Yahoo’s main web operations to Verizon has been delayed until the next quarter.
Sources told The Wall Street Journal that the SEC issued a request for documents from Yahoo in December and is looking into whether Yahoo’s breach disclosures may have violated civil securities laws. The investigation will likely focus on Yahoo’s 2014 data breach affecting 500 million users, which was announced in September 2016. Yahoo is said to have linked the 2014 breach to state-sponsored actors two years before the public disclosure. In December 2016 Yahoo disclosed a separate breach affecting more than one billion users.
The SEC has never brought a case against a company for failing to disclose a data breach, the Wall Street Journal reported, but experts said the SEC has been looking for a case to clarify guidance issued in 2011. That guidance requires the disclosure of material information about cybersecurity risks and incidents if it could affect investors, but what is “material” is still a question – a question that this case may potentially help answer.
Those two data breaches have led to speculation over the past few months of how they may impact Verizon Communication’s acquisition of Yahoo, which was valued at $4.83 billion last July. Yahoo said it is “working expeditiously” to finish the deal; nevertheless, the sale has been pushed back until next quarter.
“Yahoo has been an interesting process,” Verizon Chief Financial Officer Matt Ellis said in an interview last Tuesday with Bloomberg. “There’s been good progress, but we are still awaiting the final reports and therefore we haven’t reached any conclusions yet.”


 The most impactful, publicly known ransomware attack of late involves the
The most impactful, publicly known ransomware attack of late involves the 
 Security researchers frequently discover private data being exposed to the Internet due to technical errors such as poorly secured data backups, and this past week several new incidents along those lines.
Security researchers frequently discover private data being exposed to the Internet due to technical errors such as poorly secured data backups, and this past week several new incidents along those lines.

 It was less than a year ago that
It was less than a year ago that 
 As SurfWatch Labs noted in its annual report, organizations are increasingly
As SurfWatch Labs noted in its annual report, organizations are increasingly 


 “We uploaded the indicators to our scanning system to look for the types of things specified,” Burlington Electric Department general manager Neil Lunderville
“We uploaded the indicators to our scanning system to look for the types of things specified,” Burlington Electric Department general manager Neil Lunderville 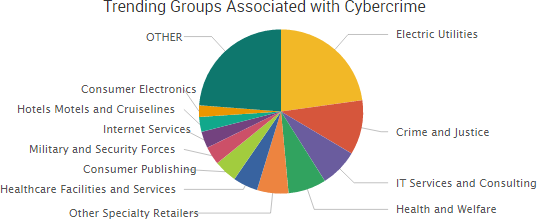
 Organizations once again are being blackmailed by threat actors who are either threatening to release stolen data or else holding data hostage unless a ransom payment is made.
Organizations once again are being blackmailed by threat actors who are either threatening to release stolen data or else holding data hostage unless a ransom payment is made.



 Looking beyond the ongoing Yahoo story, there were several unique cybercrime-related events worth noting from the past week.
Looking beyond the ongoing Yahoo story, there were several unique cybercrime-related events worth noting from the past week.
 Several stories from the past week once again highlighted the problem of malicious insiders stealing intellectual property and taking that stolen data directly to company rivals in order to give those rivals a leg up on the competition.
Several stories from the past week once again highlighted the problem of malicious insiders stealing intellectual property and taking that stolen data directly to company rivals in order to give those rivals a leg up on the competition.

 As
As 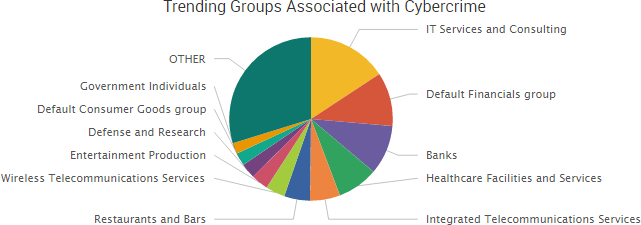

 The past week saw several legal developments involving both past breaches and possible future lawsuits.
The past week saw several legal developments involving both past breaches and possible future lawsuits.