Over the last couple weeks, several critical infrastructure cyber-events made headlines in the Industrials, Energy, and Utilities industries. Some of these targets include the German Gundremmingen nuclear reactor, the Lansing Board of Water and Light (BWL), and the Canadian gold mining firm Goldcorp. While none of these cyber-attacks resulted in chaos, they did demonstrate weaknesses within these companies.
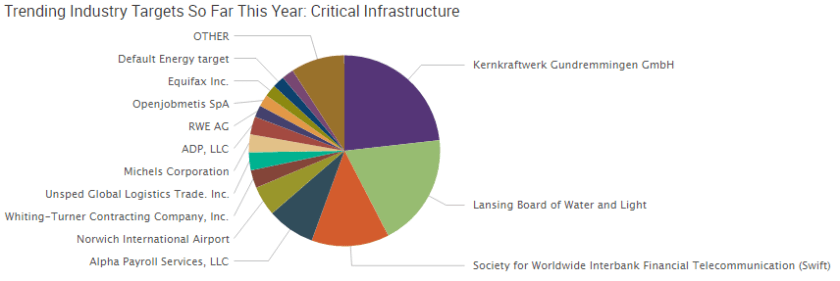
W-2 and tax-related data breaches have been trending in 2016 – this trend is also occurring in critical infrastructure. In 2016, many top trending critical infrastructure targets have suffered such a breach, including:
- Alpha Payroll Services
- Whiting-Turner Contracting Company
- ADP
- Michels Corporation
- Equifax
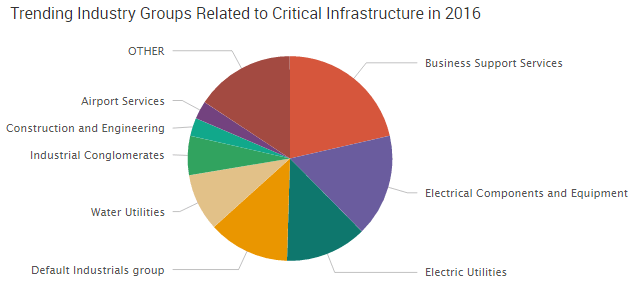
SWIFT was the software compromised in the Central Bank of Bangladesh cyber heist. As a result, business support services was the top trending industry group affected in critical infrastructure so far in 2016.
The Critical Infrastructure Cyber Threat
Attacks against critical infrastructure have occurred in the U.S.; however, these attacks have never lead to the doomsday scenario many of us fear, such as disabling power to cities or truly compromising a nuclear reactor. Most critical infrastructure attacks in the U.S. involve the loss of user data, not a takeover of key operating capabilities.
A critical infrastructure takeover has occurred in another country. In 2015, a cyber group named Sandworm Team launched an attack against the Ukrainian Power Authority. Using the infamous BlackEnergy malware, the group was able to successfully shut down power for 700,000 people over a two hour period – the first known power outage caused by a cyber-attack. The Sandworm team has attacked U.S. critical infrastructure in the past, forcing ICS-Cert to issue an alert in 2014 addressing the threat.
Attacks against critical infrastructure have been taken especially seriously by the U.S. government. In February 2013, President Barack Obama signed Executive Order 13.636, “Improving Critical Infrastructure Cybersecurity,” and Presidential Policy Directive 21, “Critical Infrastructure Security and Resilience.” The executive order and policy directive attempt to address key issues with our nation’s critical infrastructure cybersecurity, including:
- Promote information sharing with U.S. private sector
- Clearly define roles of key officials involved with critical infrastructure security
- Commit to providing assistance in the event of a data breach
- Create a framework to reduce cyber risk to critical infrastructure
- Promote innovation, research, and development of enhanced cybersecurity measures
As a result, the Department of Homeland Security (DHS) launched the Critical Infrastructure Cyber Community Voluntary Program. The goal of this program is to help enhance critical infrastructure cybersecurity and to promote the adoption of the National Institute of Standards and Technology’s Cybersecurity Framework.
Our country’s critical infrastructure suffers from the same vulnerabilities as other sectors. Valuable information is kept on databases and people are used as a bridge to that information. While the threat of a doomsday attack against our nation’s critical infrastructure remains a serious threat, traditional cybercrime is still driven by profit motive. Those in charge of critical infrastructure security not only have to be prepared for threats attempting to cause physical harm to our nation, they must also prepare for the theft of personal information, which seems to be the current trend.

