Last week Eddie Bauer became the latest in a growing string of companies to announce a major point-of-sale-related breach. All 350 North American stores were affected by malware that may have siphoned off customers’ payment card information between January and July of this year.
Not all cardholder transactions were impacted, the company said, and the breach does not include any online transactions; however, the announcement comes during the same month that Oracle MICROS, HEI Hotels & Resorts and several other companies posted similar breach announcements.
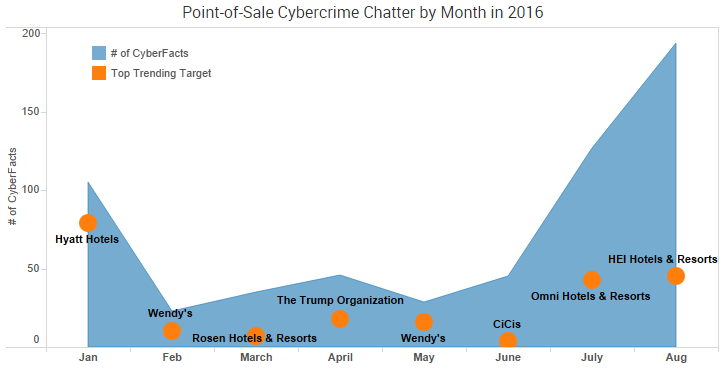
The recent surge follows a comparatively quiet period over the first half of 2016, as this chart from our Mid-Year 2016 Cyber Risk Report highlights.
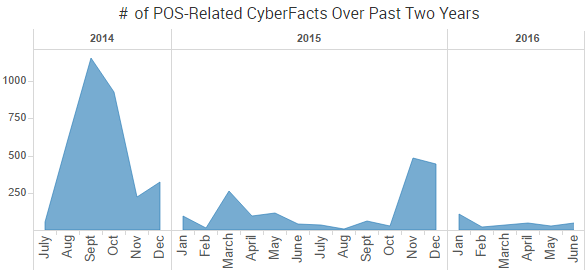
“This dip in discussion is accentuated by the extreme number of high-profile organizations affected by POS breaches in 2014, perhaps skewing the perception for what ‘normal’ levels of activity should be,” the report noted. “Point-of-sale breaches are not making as many headlines, but breaches so far this year have proven that for many organizations the associated costs are as high or higher than they have ever been.”
Revisiting that chart a month and a half later, it appears the activity level is now kicking up to match those high costs. SurfWatch Labs has collected more point-of-sale-related CyberFacts in August (through just 21 days) than any other month so far this year.
Oracle, Other Vendors Compromised
Adding to the concern around point-of-sale systems, Brain Krebs recently broke the news of a breach of hundreds of computer systems at Oracle, including a customer support portal for companies using Oracle’s MICROS point-of-sale credit card payment systems.
Sources said the MICROS customer support portal has been observed communicating with a server known to be used by the Carbanak Gang. That’s alarming since the gang is suspected be behind the theft of more than $1 billion from financial institutions in recent years.
“This breach could be little more than a nasty malware outbreak at Oracle,” Krebs wrote. “However, the Carbanak Gang’s apparent involvement makes it unlikely the attackers somehow failed to grasp the enormity of access and power that control over the MICROS support portal would grant them.”
The investigation is ongoing, and Oracle so far has not provided customers or media outlets with many answers.
To make matters worse, Forbes’ Thomas Fox-Brewster reported that several other cash register suppliers besides MICROS have been breached recently.
“It now appears the same allegedly Russian cybercrime gang has hit five others in the last month: Cin7, ECRS, Navy Zebra, PAR Technology and Uniwell,” he wrote. “Together, they supply as many as, if not more than, 1 million point-of-sale systems globally.”
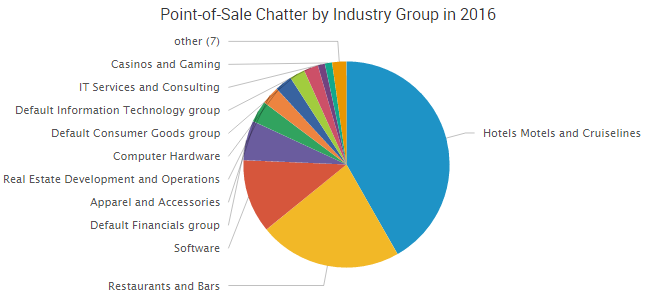
Hotels Remain Top Trending POS Target
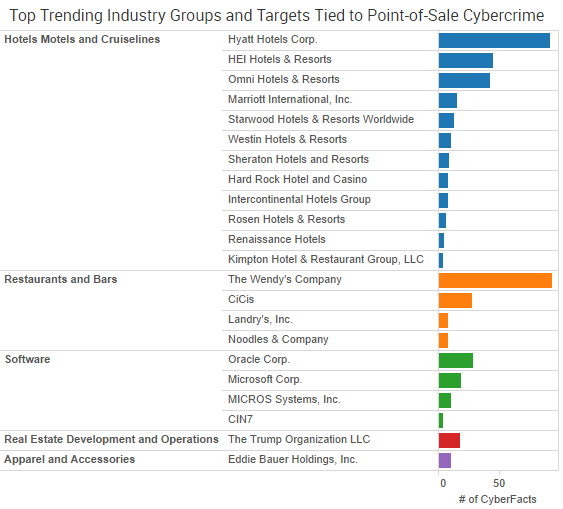
In our mid-year report, the “Hotels, Motels and Cruiselines” subgroup of Consumer Goods dominated the chatter around point-of-sale breaches, and not much has changed in the two months since that report. In fact, nearly 42% of all the point-of-sale CyberFacts collected by SurfWatch Labs so far this year have fallen into that group.
The top trending point-of-sale target this month is HEI Hotels & Resorts, which announced a breach involving 20 hotels on August 12. The malware was discovered in June on point-of-sale systems used at restaurants, bars, spas, lobby shops and other facilities, according to Reuters. Twelve Starwood hotels, six Marriott International properties, one Hyatt hotel and one InterContinental hotel were impacted.
If those names sound familiar, it’s because several of them have already made news for data breaches of late, including Hyatt in December 2015 and Starwood in January 2016.
Other data breaches this year involving hotels include Kimpton Hotels, Hard Rock Hotel & Casino Las Vegas, Rosen Hotels & Resorts and the Trump Hotel Collection.
Although the various incidents that have been announced in recent weeks have not been explicitly connected by either researchers or law enforcement, the breach notice from Eddie Bauer did signify that other organizations have been targeted with a similar campaign.
“Unfortunately, malware intrusions like this are all too common in the world that we live in today,” the company wrote. “In fact, we learned that the malware found on our systems was part of a sophisticated attack directed at multiple restaurants, hotels, and retailers, including Eddie Bauer.”
Other experts such as Gartner fraud analyst Avivah Litan have speculated that the breach at Oracle “could explain a lot about the source of some of these retail and merchant point-of-sale hacks that nobody has been able to definitively tie to any one point-of-sale services provider.”
At the moment many questions remain, but if these investigations lead to the discovery of further compromises, expect to see more breach announcements and more payment card information being sold on Dark Web markets in the months to come.


It’s such a lame that pos systems aren’t safe at all today. From the one hand pos makes business more simple but from the other you can get lots of problems.
LikeLike